Cho em góp vui tí nhé.
Virus (máy tính)
Bách khoa toàn thư mở Wikipedia
Trong
khoa học máy tính,
virus, còn gọi là
virus máy tính, là một loại
chương trình máy tính được thiết kế để tự nhân bản và sao chép chính nó vào các chương trình khác (truyền nhiễm tính) của máy tính. Virus có thể rất nguy hiểm và có nhiều hiệu ứng tai hại như là làm cho một chương trình không hoạt động đúng hay huỷ hoại bộ nhớ của
máy tính (độc tính).
Có loại virus chỉ làm thay đổi nhẹ
màn hình nhằm mụch đích "đùa giỡn" nhưng cũng có thứ tiêu huỷ toàn bộ dữ liệu trên các
ổ đĩa mà nó tìm thấy. Một số loại virus khác lại còn có khả năng nằm chờ cho đến đúng ngày giờ đã định mới phát tán các hiệu ứng tai hại. Hầu hết các loại virus được phát triển chỉ nhắm tấn công vào các hệ điều hành
Windows vì thứ nhất thị phần của các
hệ điều hành này lên đến khoảng 90%, và thứ hai là hệ điều hành
Windows không an toàn như các hệ điều hành dựa trên nhân
Linux.
Tuỳ theo chức năng hay phạm vi hoạt động, người ta có nhiều cách phân loại virus.
Virus lan truyền qua thư điện tử
Đại đa số các virus ngày nay thuộc vào lớp này. Lí do là virus có thể tự tìm ra danh sách các địa chỉ
thư điện tử và tự nó gửi đi hàng loạt (
mass mail) để gây hại hàng triệu
máy tính, làm tê liệt nhiều cơ quan trên toàn thế giới trong một thời gian vô cùng ngắn.
Một nhược điểm của loại virus này khiến chúng ta có thể loại bỏ nó dễ dàng là nó phải được gửi dưới dạng đính kèm theo thư điện tử (
attached mail). Do đó ngưòi dùng thường không bị nhiễm virus cho tới khi nào tệp virus đính kèm được mở ra (do đặc diểm này các virus thường được "trá hình" bởi các tiêu đề hấp dẫn như sex, thể thao hay quảng cáo bán phần mềm với giá vô cùng rẻ.)
Nhược điểm thứ nhì của loại virus này là nó phải là tệp mệnh lệnh tự thi hành (
self executable file). Trong hệ thống
Windows có một số kiểu tệp có khả năng này, chúng bao gồm các tệp có đuôi (
extension) là .exe, .com, .js, .bat,... và các loại script. (Lưu ý, chữ "mệnh lệnh tự thi hành" là để phân biệt với các tệp mệnh lệnh phải được gọi qua một chưong trình trung gian như dll, vxd.)
Trước đây, để tìm bắt các tay
tin tặc chuyên phát tán virus thì
FBI hay
Interpol thường dựa vào danh mục người gửi để truy ngược về người phát tán virus đầu tiên mà bắt giữ.
Tuy nhiên, loại virus này không phải là không có ưu điểm. Thứ nhất, nó có thể lợi dung khuyết điểm
làm tròn dung lượng hiển thị của hệ thống (Ví dụ: 2,01K thành 2K) để ẩn những con virus
Dung lượng nhỏ khi gửi. Thứ hai, nó có thể giấu một phần của tệp tin gửi và hiển thị đuôi file và chỉ cần người dùng
liên kết đến file đó là bị dính virus.
Danh sách các đuôi tệp có khả năng di truyền và bị lây nhiễm
Các tập tin trên hệ điều hành Windows mang đuôi mở rộng sau có nhiều khả năng bị virus tấn công.
- .bat: Microsoft Batch File
- .chm: Compressed HTML Help File
- .cmd: Command file for Windows NT
- .com: Command file (program)
- .cpl: Control Panel extension
- .doc: Microsoft World
- .exe: Executable File
- .hlp: Help file
- .hta: HTML Application
- .js: JavaScript File
- .jse: JavaScript Encoded Script File
- .lnk: Shortcut File
- .msi: Microsoft Installer File
- .pif: Program Information File
- .reg: Registry File
- .scr: Screen Saver (Portable Executable File)
- .sct: Windows Script Component
- .shb: Document Shortcut File
- .shs: Shell Scrap Object
- .vb: Visual Basic File
- .vbe: Visual Basic Encoded Script File
- .vbs: Visual Basic File
- .wsc: Windows Script Component
- .wsf: Windows Script File
- .wsh: Windows Script Host File
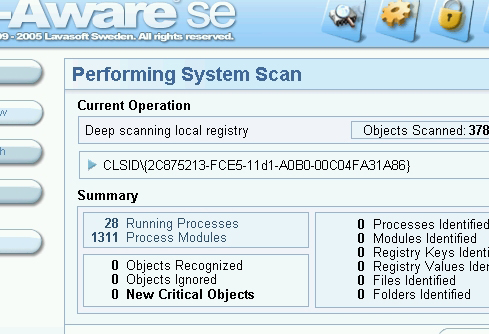
- .{*}: Class ID (CLSID) File Extensions
Ngày nay đã có rất nhiều loại virus mới tự bản thân chúng có thể "ăn cắp" tên và địa chỉ thư điện tử của các chủ hộp thư khác để mạo danh mà gửi các đính kèm tới các địa chỉ chứa trong các hộp thư của họ.
Do đó,
ngay cả các thư điện tử có địa chỉ gửi từ người thân quen cũng không chắc là không chứa các đính kèm có thể là virus. Nạn nhân điển hình của việc lan truyền virus kiểu này thường từ các hộp thư điện tử miễn phí vì các hộp thư này thường không cung cấp đầy đủ các dịch vụ bảo vệ tối đa cho thân chủ.
Dựa vào đó, một lời khuyên tốt nhất là đừng bao giờ mở các tệp mệnh lệnh mới qua thư điện tử trừ khi biết rõ 100% là chúng không chứa virus.
Lưu ý:
Trong các chương trình hộp thư loại cũ (
Outlook 95 chẳng hạn) hệ điều hành, bởi mặc định, sẽ không hiển thị đuôi của các tệp đính kèm qua thư điện tử nên cần phải cài đặt lại để tránh lầm tưởng một tệp có đuôi là .txt.exe thành đuôi .txt (vì khi đó hệ điều hành tự động dấu đi cái đuôi exe). Thay vì nhìn thấy tên tệp là "love.txt.exe" thì người đọc chỉ nhìn thấy "love.txt" và lầm rằng đó chỉ là tệp kí tự thường, nhưng kì thực nó là
virus Love.
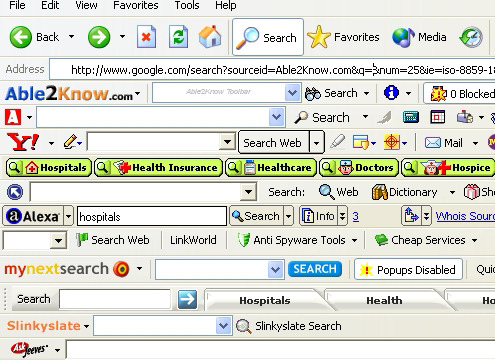
Virus lan truyền qua Internet
Khác với loại lan truyền qua thư điện tử, virus loại này thường ẩn mình trong các chương trình lưu hành lậu (
illegal) hay các
chương trình miễn phí (
freeware, shareware). Thật ra không phải chương trình lậu hay chương trình miễn phí nào cũng có virus nhưng một số tay hắc đạo lợi dụng tâm lý "tham đồ rẻ" để nhét virus vào đấy.
Loại này thường hay nằm dưới dạng .exe và nhiều khi được gói trong .zip.
Các
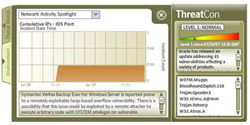
hệ điều hành mới ngày nay có khả năng tự khởi động và cài đặt một
phần mềm ngay sau khi tải về máy. Tính năng này rất tiện lợi nhưng cũng vô cùng tai hại nếu nhỡ chương trình tải về có chứa virus thì rõ ràng người tải về đã "cõng rắn cắn ... máy nhà".
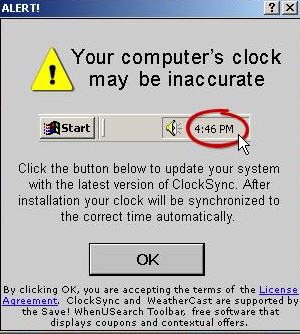
Lời khuyên:
Đừng bao giờ cho phép (đồng ý nhấn nút
OK mà không cần biết mình đã làm gì!!!) mở tệp tin ngay lập tức sau khi tải về mà
trước nhất phải kiểm qua virus.
Các virus cổ điển
Virus đầu tiên là phát minh của một thiếu niên ở
Anh. Nó chỉ truyền được qua đường
mạng và các thiết bị chứa dữ liệu như
đĩa mềm do kết quả của việc sử dụng chung đĩa mềm,
CD ROM,
đĩa ZIP/ZAP hay
băng từ. Virus nổi tiếng trong lich sử
máy tính của loại này là
virus Stealth. Nó có khả năng thay đổi ngay cả chức năng của
BIOS. Ngày nay, Stealth vẫn còn nhưng đã được biến dạng thành một trong hai loại kể trên.